Ellef Prestsæter: Readers of Concreta, beware! … Engaging with you, Asger, in the context of this special issue on Vandalism and Iconoclasm calls for a strict demarcation between vandalism on the one hand and iconoclasm on the other. While the Scandinavian Institute of Comparative Vandalism (SICV) connects you intimately with the concept of vandalism you are anything but iconophobic. Your notorious détournements or modifications provide a case in point: there clearly is a brutally destructive moment in overpainting these tableaus bought at flea markets, but the point was never to annihilate or make fun of them. You were rather driven by a profound interest for the “popular” art form these pictures represented. The overpainting is a form of resurrection or remobilization, or, on a somewhat more prosaic note, a form of image analysis. And the endpoint was always a new image. Whatever you may have meant by “vandalism”, your practice was always rooted in an engagement with, and even a love for, images. The iconophilic vandalist? The notion carries a certain attraction …
Asger Jorn: An interest in dispersed attention, such as the one modern art has shown throughout this century, may contribute to the deterioration of culture’s authoritarian patent makers, and surely it is this practice you would call comparative vandalism.
Michael Murtaugh: But …
AJ (ignoring the interruption): Détournement is a game born out of the capacity for devalorization. Only he who is able to devalorize can create new values. And only there where there is something to devalorize, that is, an already established value, can one engage in devalorization. It is up to us to devalorize or to be devalorized according to our ability to reinvest in our own culture.
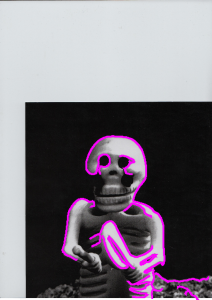
EP: Michael, visually, the images produced through the contour-tracing scanner echo Jorn’s modifications as well as the images in the so-called tongue-book —La Langue verte et la cuite from 1968 — where Jorn assembled black and white images from around the world and colored the tongues in all the images. This similarity calls for a comparative analysis, don’t you think?
MM: Consider what happens when you run an image analysis procedure such as an edge detection or a (SIFT*) feature extractor, and then use a conventional means of visualizing the results drawnon top of the original. The result is an image dense with markings, edges of figures traced with the brutal pixelized edge of a computed curve or dotted with swarms of circular markers of various sizes and positions throughout the image at various points of (algorithmically determined) interest. The marks typically number from tens to hundreds. Visually, the language of the algorithmically annotated image resonates with the vandalized image, the political poster with sprayed-on beard or mustache, the marketing billboard covered with elements crossed out or covered by graffiti tags. There is an essential difference however: where the billboard vandal challenges the authority of the image (both of those depicted and the forces that arrange to place them in public), the marks of the algorithm carry themselves an authority borne from the often impenetrable layers of technique and software employed. On top of this, such techniques may well be further allied to authority by patents, software licenses, and other aspects of law. Furthermore, the images most frequently subjected to the algorithmic processes of analysis are typically banal ones, themselves collected by agents of authority and typically recorded with their subjects (relatively) unaware of their being taken. For instance, the closed circuit surveillance system in a shopping center or laundromat, or the passport control agent’s webcam. Computational vandalism aims to challenge the authority of the algorithm and uses computation both as a means and a subject of critical investigation. It aims to expose the values enshrined in algorithms, to consider alternatives, and to feed them back upon themselves to make these processes more apparent in their operation, as well as to activate them as tools to investigate other kinds of images and contexts from their conventional uses.
Nicolas Malevé: You are right to underline the authority of the algorithm. It is nevertheless interesting to see that this authority is granted under a very specific condition. The algorithm must in the end confirm human perception. I always see a visual algorithm as a sort of Hercule Poirot on a crime scene. Where his assistant Captain Hastings will immediately decode the semantic layer, the obvious clues, the motives, Poirot always seems concerned with absurdly pointless details: a slight change of color in a carpet, the position of a finger, etc. Poirot seems to embody the coolness of media archeology, indifferent to content. Let’s think of the SIFT algorithm, how it looks into extremely narrow fragments of an image to find patterns that could identify an image even when it is rotated. When we look at the regions of the images selected by the algorithm, they seem completely secondary to the human observer. But, in the end, if we make a search for similar images, the results returned by this algorithm seem to match very well what a human would have picked up. In every Hercule Poirot ending, the tour de force is to make a match between all these apparently absurd little clues and a narrative where the murderer is punished and the social order is confirmed. In every operation of computer vision, there is this expectation that the gap between human perception and computer perception will be filled. But what if it isn’t? What if it reveals that there is a zone of intersection between human perception and computer vision, and that the contours of this zone are problematic, fluctuating? Computational vandalism is what introduces us to a world with a proliferation of powerfully meaningless little clues that do not point towards any murderer. Nobody is punished in the world of computational vandalists, but its visual structure is denser. Computational vandalism is Agatha Christie smoking Asger Jorn’s cigar.
From “Vandalist Iconophilia,” a conversation between Michael Murtaugh, Nicolas Malevé, Ellef Prestsæter, Matthew Fuller and Asger Jorn published in Concreta 5/2015.